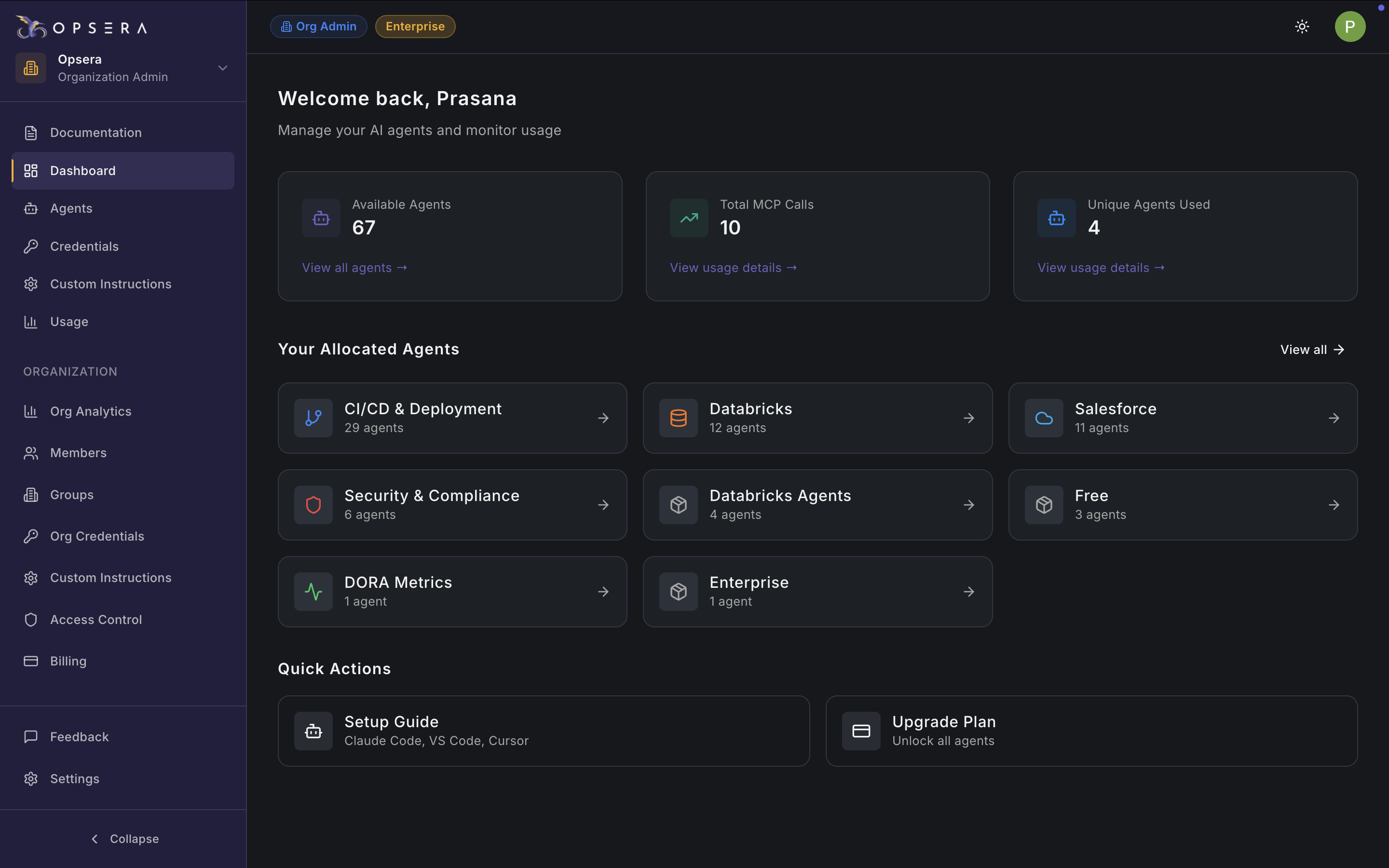
| Section | Description | Why It Matters |
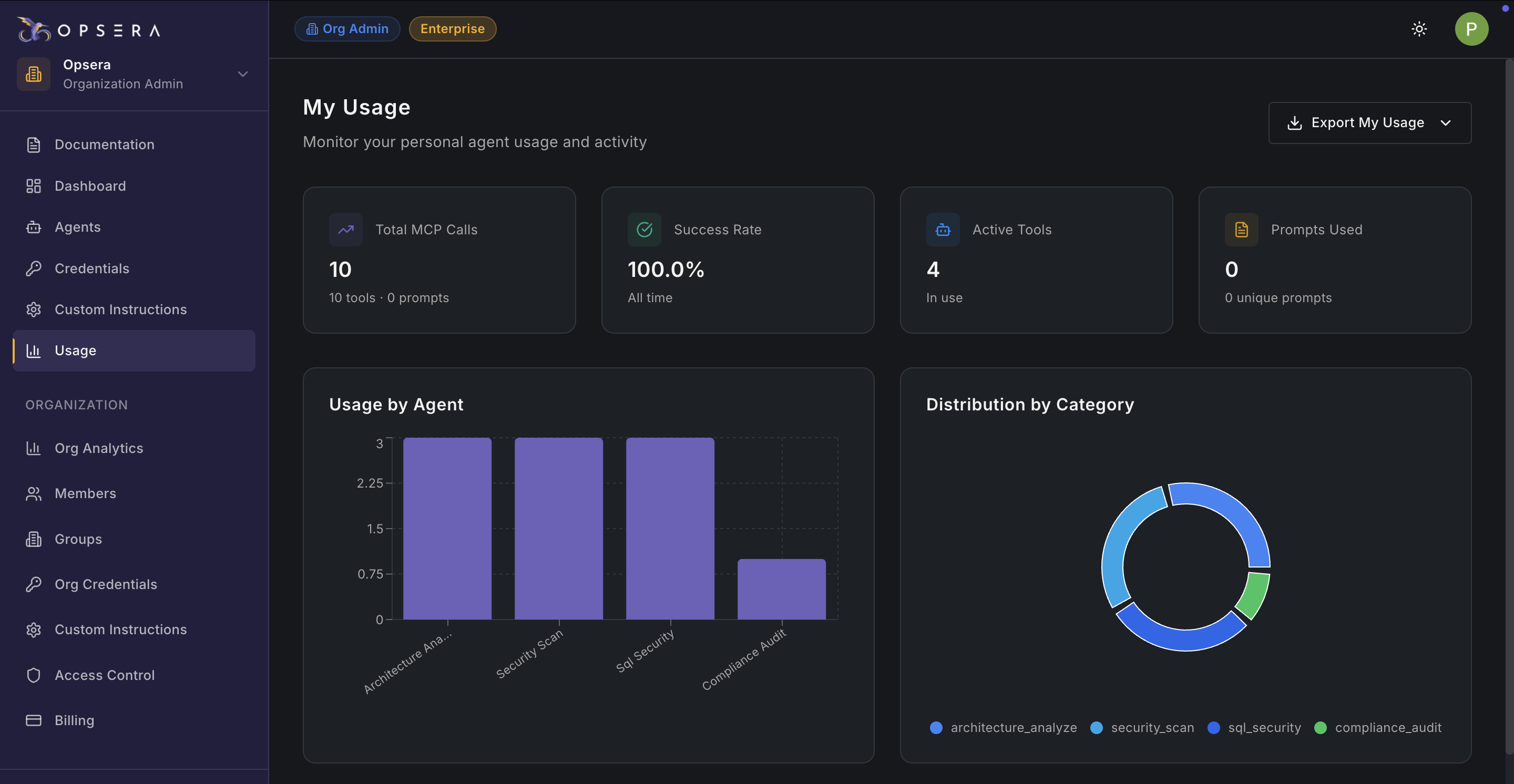
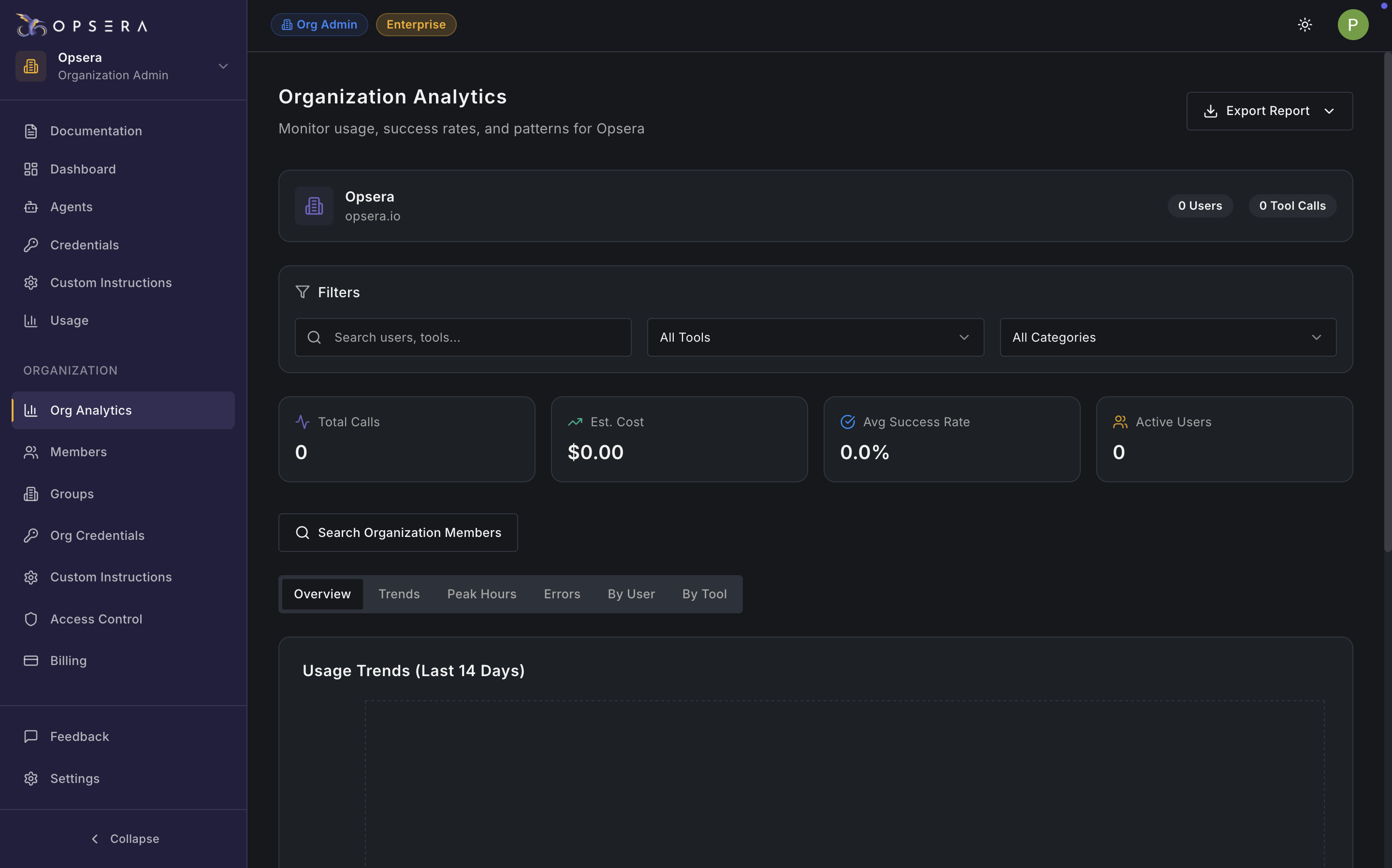
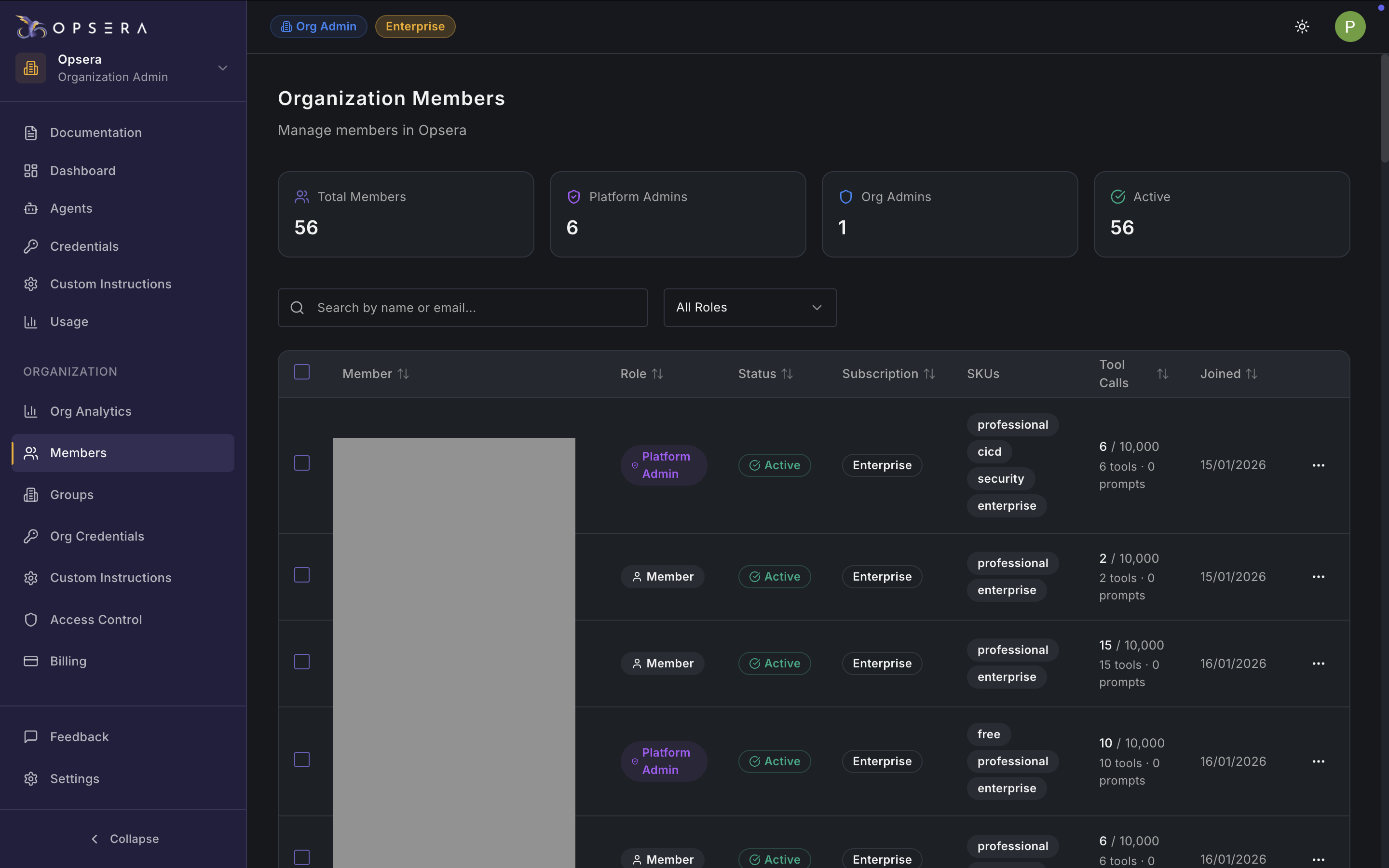
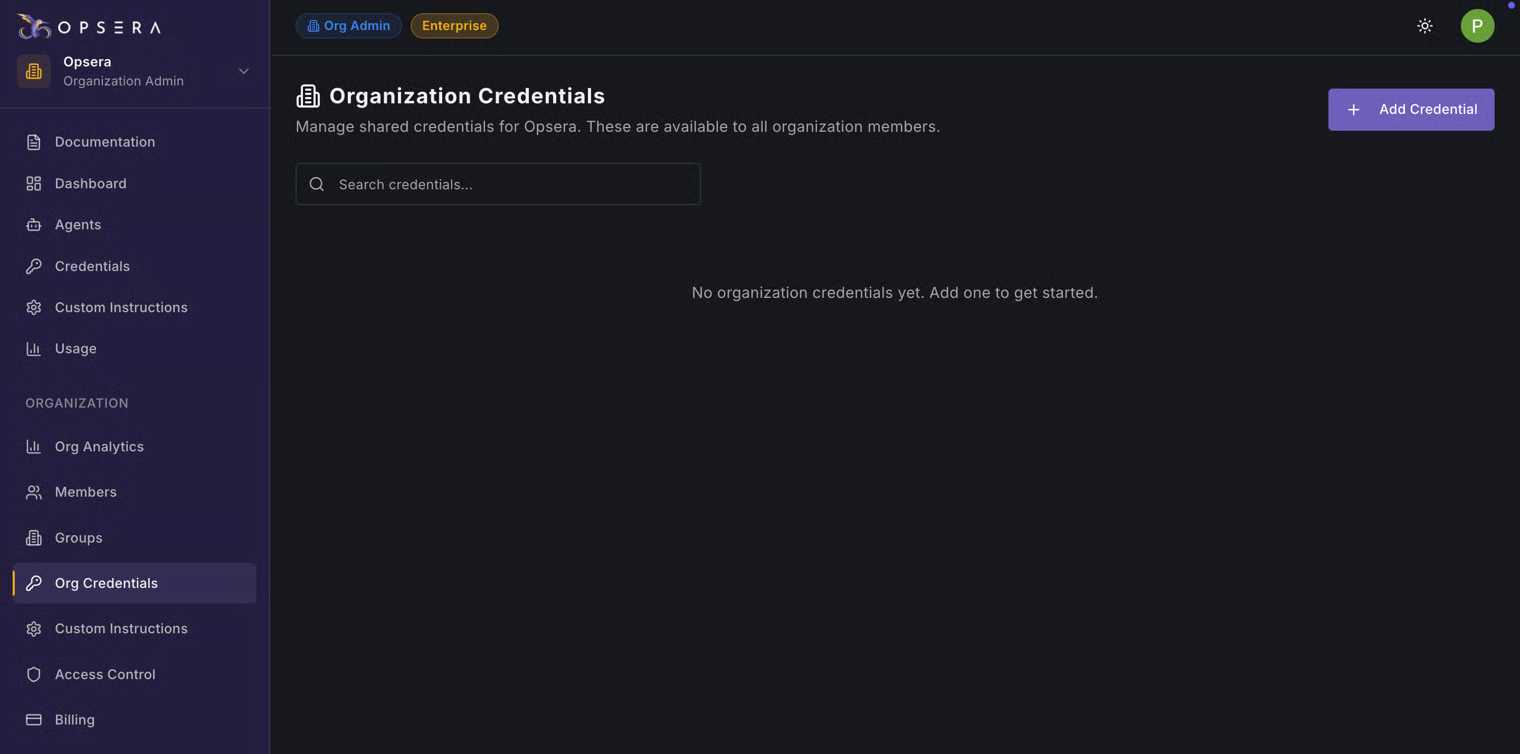
| Summary Metrics | Total number of tool invocations across all agents | Measures overall platform usage and adoption |
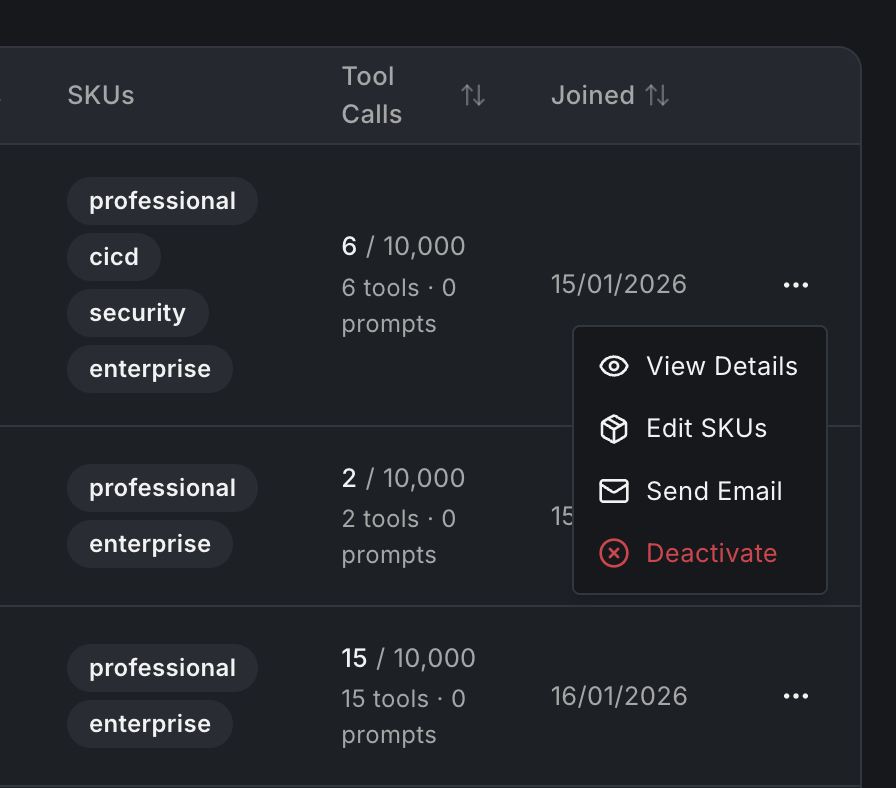
| Percentage of successful tool executions | Indicates execution reliability and system health |
| Number of tools currently in use | Shows breadth of agent adoption |
| Count of unique prompts executed | Helps understand usage diversity |
| Usage by Agent (Bar Chart) | Visualizes how often each agent is used | Identifies heavily used vs underused agents |
| Side-by-side usage comparison across agents | Highlights optimization or enablement opportunities |
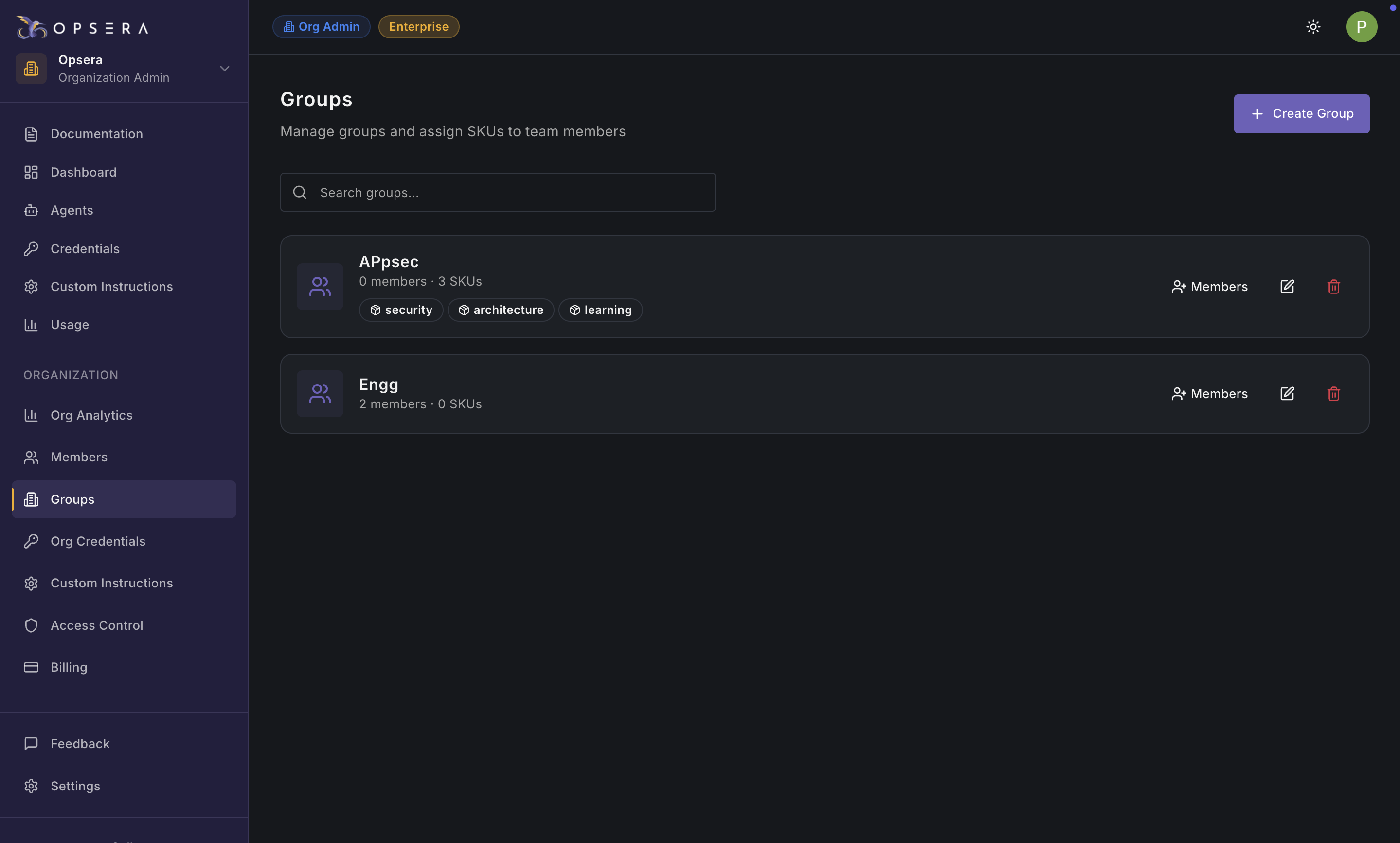
| Distribution by Category | Usage related to architecture and design analysis | Tracks strategic planning and design automation |
| Usage of security-focused agents | Measures security automation adoption |
| Usage of database and SQL security tools | Identifies database risk management activity |
| Usage of compliance and audit agents | Supports governance and compliance tracking |
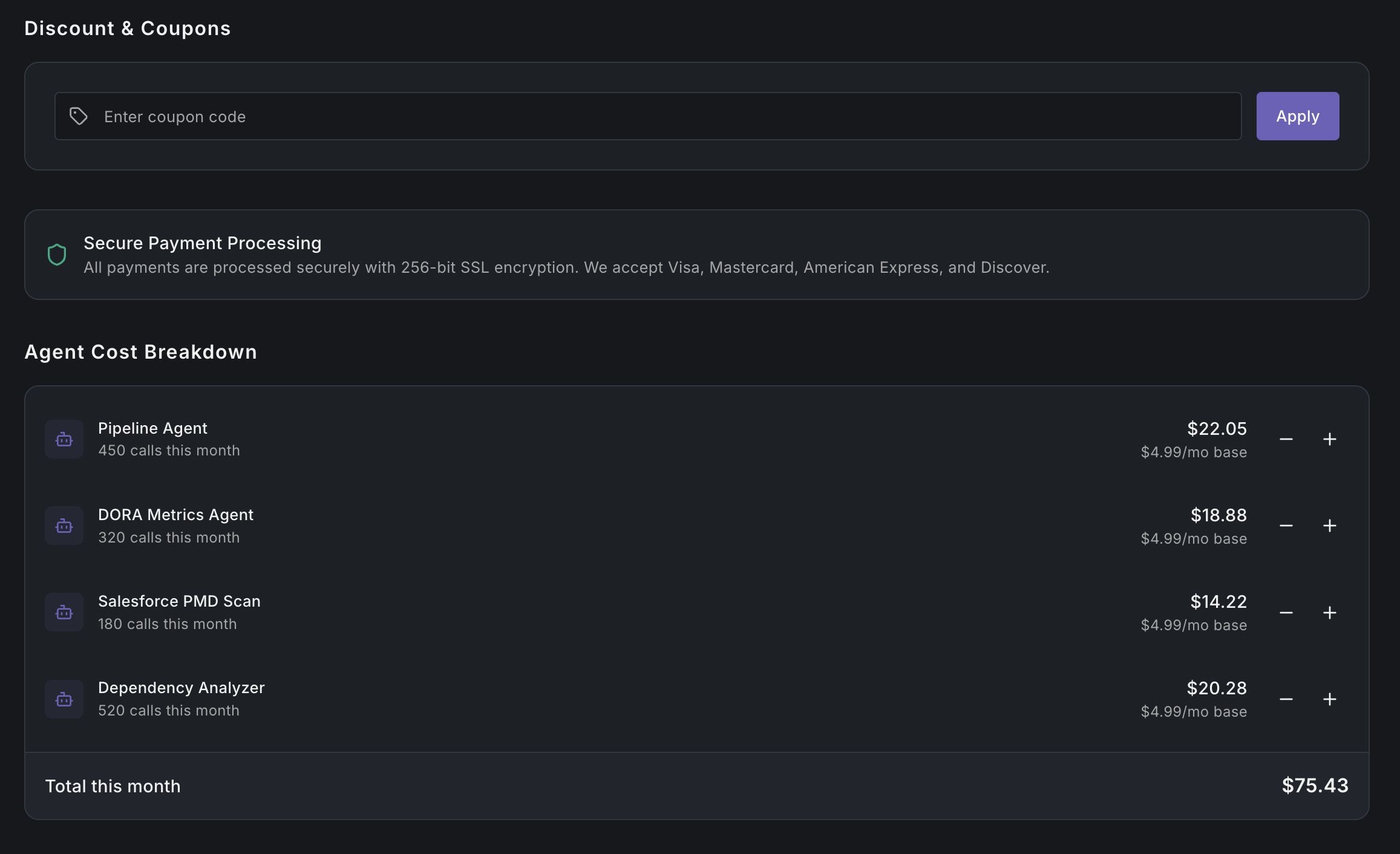
| Detailed Tool Table | Number of times each tool was executed | Shows tool demand and frequency |
| Execution success percentage per tool | Helps diagnose reliability issues |
| Average time taken per execution | Identifies performance bottlenecks |
| Most recent execution timestamp | Highlights stale or unused tools |
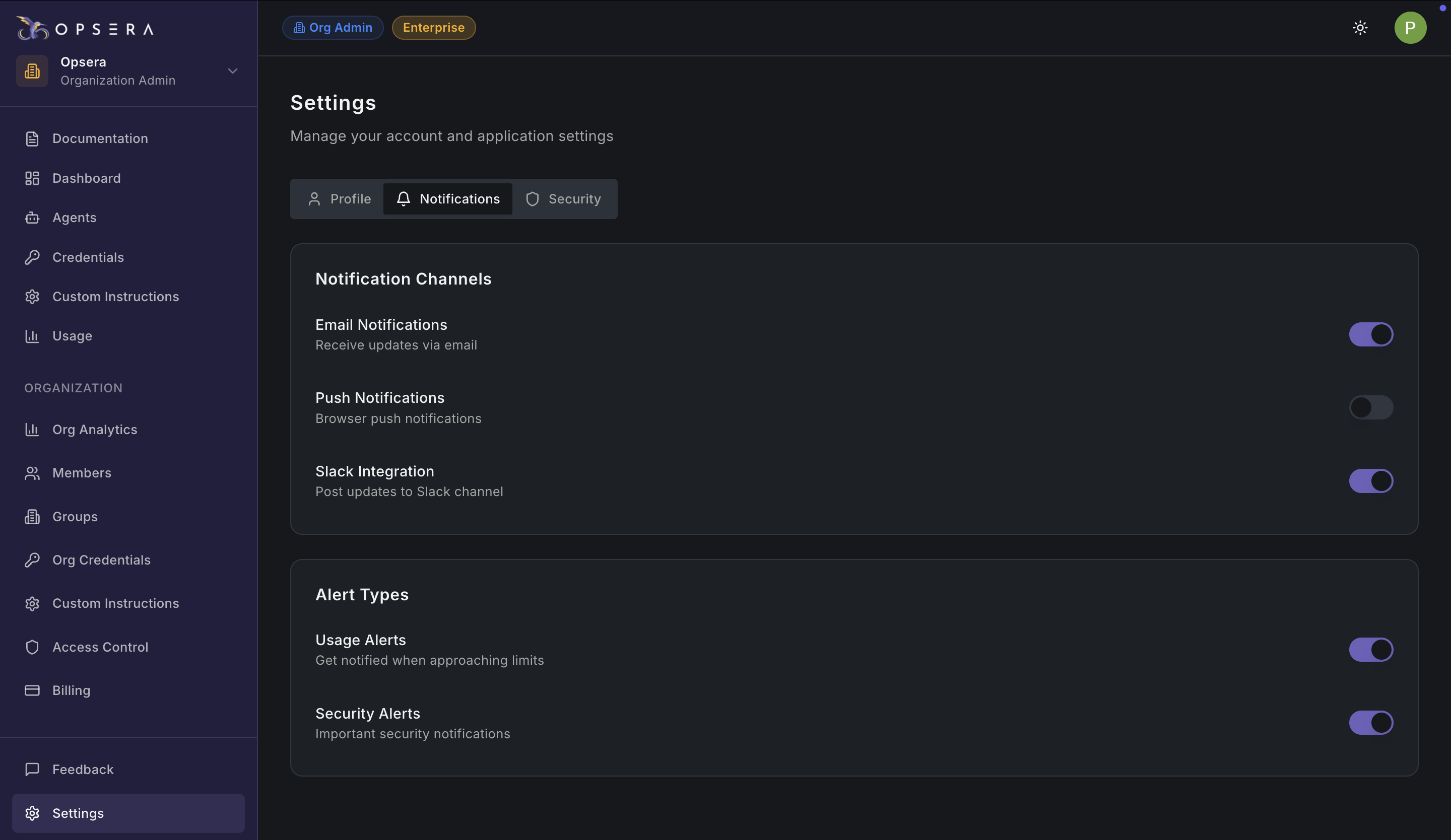
| Operational Insights | Uses execution data to detect issues | Improves tool reliability and tuning |
| Correlates usage with business value | Supports leadership reporting |
| Identifies candidates for deeper automation | Guides future optimization efforts |